This is an adapted version of Stu's old dissertation from 2018. We felt it was well worth a public outing, with updates relevant to 2021. Growth hacking is a very dirty word, and has dropped from use amongst serious SEOcompanies. But the idea of giving Google want it wants to boost links and traffic is still 100% valid. For example for most websites and SEO problems, simply "thinking like Google", usually begets some interesting and usually successful ideas. Stu's investigation below is interesting as it was written at the waning of the importance, and use of the term "Growth Hack"...
1. Introduction
1.1 Overview
Search engine optimisation (SEO) is the “process of designing a website to appear early in search engine result pages”; a form of e-marketing and digital advertising for websites. Traditional SEO is comprised of a number of techniques designed to increase web traffic to websites (Lee, Jang, Lee & Oh, 2016) through promoting themselves to search engines such as Google.
With these facts, traditional SEO can be described as a form of digital marketing targeted towards search engines, rather than end-users. In 2010, digital marketer Sean Ellis coined the new term ‘growth hacker’ to describe a digital marketing role in which their only purpose is to grow (Ellis, 2010). This was expanded on by Andrew Chen, startup advisor and investor, in 2014 to describe someone who does everything possible to “attract new clients for [a] product or service” (Chen, 2014).
Household company names such as Groupon and Airbnb boast massive success stories in which growth hacking has increased traffic (Holiday, 2013), but the term has also garnered much controversy. Some techniques now associated with growth hacking are suggested to have had questionable ethics, particularly Airbnb, in how they were carried out (Ellis, 2014), whereas some critics question its success rate (Fishkin, 2018).
In an age where “75 percent of venture-backed companies never return cash to investors” (Hoque, 2012, Article subtitle), can growth hacking techniques aid startup business owners in fulfilling their visions, or is the methodology just a marketing buzzword?
1.2 Aims
- Investigate growth hacking’s uses as a search engine optimisation (SEO) methodology and discuss its comparisons to traditional SEO techniques
- Identify any benefits and drawbacks to implementing growth hacking to increase web traffic
- Discuss the ethical issues associated with some growth hacking techniques
1.3 Objectives
- Conduct a thorough review of appropriate literature to establish the key issues of growth hacking
- Determine appropriate examples of SEO techniques to develop utilising growth hacking
- Provide potential solutions with which to measure growth hacking’s successes and failings in websites
2. Literature review
2.1 Introduction to Growth Hacking
Growth hacking, as defined by Ellis, describes a particular role in digital marketing in which the hacker’s sole purpose is to drive growth for a company. From this, it can be derived that this type of marketing is irrespective of any product. In the context of this research, the term ‘hacking’ is used similarly to how it is defined in the web informational RFC 1983: “A person who delights in having an intimate understanding of […] computers” (Malkin, 1996). Often misued to define ‘cracker’, “an individual who attempts to access computer systems without authorization” (Malkin, 1996), hacker simply means to have an innate knowledge of computing while not necessarily meaning to have malicious intentions. To this end, it appears that the definition of growth hacker could be described as someone with an extensive knowledge and interest in ‘growth’, which corroborates with Ellis’ definition. However, as discussed later in this paper alongside ethics, the term growth hacker is also misused to describe somewhat potentially malicious actions in how it is implemented. Looking at data provided by Google Trends (2018), the popularity of the term ‘growth hacker’ in Google searches has seen a rise since its coining in 2010, with a spike in searches after Andrew Chen’s blog article praising growth hacking in 2014 (see Figure 1).
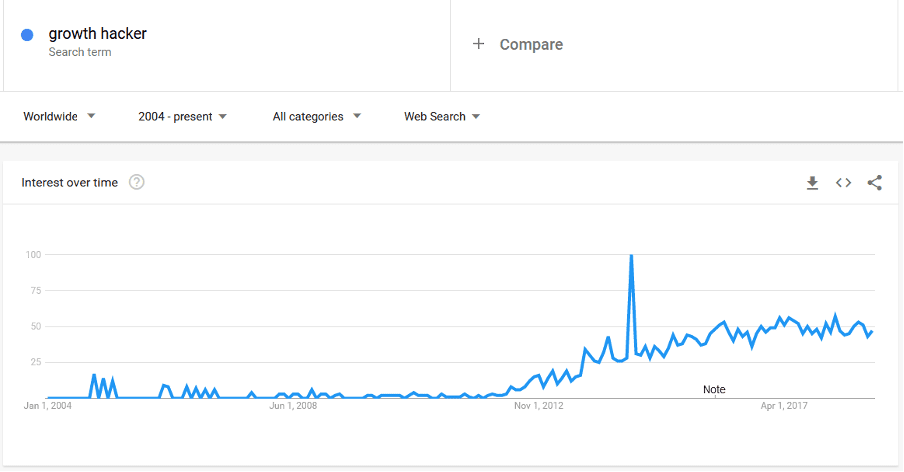
Figure 1. Interest[i] for the term 'growth hacker' in Google searches from 2004 to 2018. Data source: Google Trends (2018)
Some growth hacking techniques are applied to websites, and consequently it is fair to describe elements of growth hacking as an SEO methodology – its purpose being to drive traffic to a company’s website. The most notable growth hacking success stories come from its use in SEO on websites. Hotmail is commonly cited as one of the earliest uses of growth hacking on the web (Fishkin, 2018) and was as simple as adding an email signature to the bottom of each email sent through the service, which read “Get your free email at Hotmail” (Lerner, 2017). This created a “viral loop” (Penenberg, 2010), meaning – using Hotmail as an example – as more email was sent, more users would be exposed to Hotmail. More accounts would be created as a result, and these new users would send more email containing the same signature. Hotmail’s user base grew exponentially, and, crucially, it could be measured effectively through the use of referral links. More recently, Groupon utilised social media as a growth hacking technique to increase web traffic. In order for users to gain access to a particular product or deal, a specific number of users has to share the webpage on a social media platform (Peters, 2014), thus exploiting the digital connections between people to advertise the website and drive growth.
Looking at Hotmail as an example, it is clear that while the concept is relatively new, some techniques now associated with growth hacking have been in use since the late 1990s. One could argue that this undermines the idea of growth hacking as a new, alternative, take on SEO and digital marketing; despite the recent popularity, growth hacking is not necessarily a new methodology.
2.2 Growth Hacking in a comparison with traditional SEO practices
Search engines are web-based applications that use a query to retrieve results from a database. In statistics by Comscore across a variety of search engines (Lella, 2016), 16.8 billion search queries were made in February 2016 in the USA – on desktop devices alone. As a result of this apparent hunger for information, society has seemingly become an “attention economy” as theorised by Goldhaber (1997). Organisations must compete to receive user attention, and search engines are the aggregators of this commodity (Halavais, 2018). Traditional SEO as defined in this paper means to optimise a particular website in order to appeal to search engines. By doing so, search engines will more willingly serve the website in question to more users in a more noticable position, and in turn the website will receive more traffic. Google, the largest online search engine with a share of 64% of the total market (Lella, 2016) (see Figure 2), states in its SEO documentation that it “return[s] the results we believe are the most relevant to the user” using over 200 factors, and ranks them programmatically (Google, 2018) – though these factors are mostly undisclosed and a set of vague guidelines are published instead.
Figure 2. Explicit core search share (%) (desktop devices only). Data collected by Comscore (Lella, 2016).
It is clear that control remains firmly with Google and other search engines in deciding how high up the index each website is positioned, and website administrators are not guaranteed high rankings despite how well their websites are marketed. One major SEO technique is known as back linking. This is where external, or third-party, websites contain links to the original website. This appeals to search engines as it acts as a “vote of confidence” (Moz, 2018) that the original website contains quality content. This is perhaps a major drawback for some websites, such as startups, that need quick growth in terms of traffic and no backlinks from other websites. This is a traditional SEO practice that is rectified by a seemingly unethical growth hacking technique known as ‘link farming’, which is discussed more in-depth later in this paper in Section 2.4. Techniques such as this act to deceive the search engine ranking algorithms in order to improve a website’s SEO, despite being in violation of search engine terms of service. This provides more insight into how growth hacking differs from traditional SEO practices; growth hacking’s definition appears to show a merciless approach to driving web traffic, where the hacker is focused on growth and nothing else. While traditional SEO practices focus on appealing to search engines by following rules to improve a website’s online exposure, growth hackers perhaps ignore these rules and see the search engines as nothing more than a platform with which traffic can be sourced.
Looking at data provided by Google Trends (2018), it is evident that the interest for searches of the term ‘search engine optimisation’ has declined since 2004, perhaps highlighting the decreasing importance of appealing to search engines as methodologies such as growth hacking are discovered. It appears that, generally, website administrators had shown a lack of interest for SEO, up to a point in October 2015 where interest for the term ‘growth hacker’ was higher. At this point, however, interest for SEO made a dramatic return and spiked up to a popularity of 41. Perhaps this reinforces the idea that growth hacking, as a concept, had matured and website administrators found SEO to be more beneficial. It could also be that as a consequence of the rise in popularity of growth hacking, more users found themselves invested and more interested in SEO as a whole, and therefore an interest was regained. With all that said, at the same time as the resurrected interest in SEO, Google made an improvement to their data collection algorithm; as a result, it is difficult to explain exactly why the trends have acted in such a way (see Figure 2).
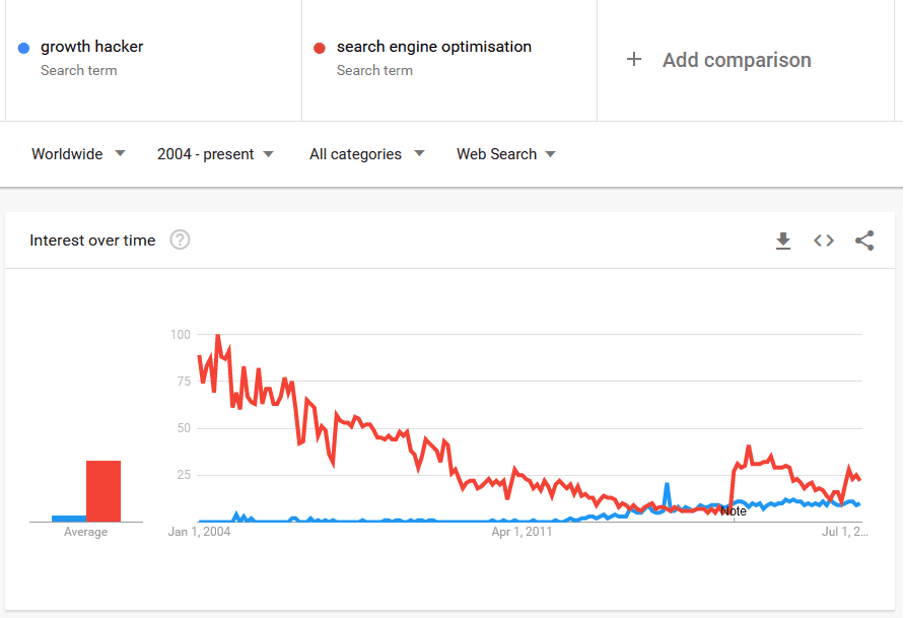
Figure 2. Interest[ii] for the term 'growth hacker' in comparison to the term ‘search engine optimisation’ in Google searches from 2004 to 2018. Data source: Google Trends (2018)
While both traditional SEO practices and growth hacking exist to acquire traffic to a particular website, their techniques and implementations appear to be completely different. Therefore rather than simply choosing one or the other, a company interested in generating growth may decide to implement both methodologies – growth hacking to attract traffic quickly, and traditional SEO practices to begin a foundation on which to slowly build an online web presence on search engine indexes. As far as growth hacking is concerned, techniques vary in their effectiveness and ethics, so such a company could find it important to consider the benefits and drawbacks of each technique individually.
2.3 Common techniques and measuring their effectiveness
While the approaches vary in techniques used to growth hack, some common themes appear to be present. For instance, almost all techniques refer to the use of an external website or platform in order to source a userbase. Social media platforms such as Facebook can be ideal for these purposes, as in Q2 2018 Facebook had a total of over 2 billion monthly active users (Statista, 2018). One common growth hacking technique employed by many businesses including Groupon implement social media sharing in order to drive web traffic; specifically in Groupon’s case, some deals would be locked until a specific number of users had shared the web page. Irrespective of the product or platform, this is an almost guaranteed method of gaining traffic.
A previously mentioned tactic called ‘link farming’ is a growth hacking technique which means to have seemingly unrelated or paid for websites create backlinks to one website in order to improve the website’s SEO (Tillison, 2017) and deceive a search engine’s ranking algorithm. A common implementation includes participating in ‘link schemes’, where a company pays for or exchanges links to be created on third-party websites (Google, 2018). Another, more covert approach, involves hosting documents such as PDFs online which contain links to the website in question. As users see these documents, the quality of the backlinks improve.
In order to avoid breaking search engine terms of service and regulations, some of the more ethical growth hacking techniques simply bypass these services altogether. Like the previously mentioned case study for Groupon, Dropbox implemented a similar technique in which if a user shares the website to a social media network, they are rewarded with additional storage space on their account (Arora, 2016). This implementation was most likely verified by a ‘bot’, here meaning a computer script, which detects the use of particular string or link (such as a hashtag) in social media posts associated with the company. Once the account in question has had their post verified, storage was awarded. An additional implementation of a similar feature included directly referring another individual to create an account, in which, utilising a web form, the user could send emails or share to a social network with a referral link (Peters, 2014). This implementation is arguably more powerful than a traditional advertisement as it includes a personal recommendation by the user that shared the webpage.
Tinder, a speed-dating app with a heavy focus on its use of geo-location and simple gesture-based user interface, implemented a growth hacking technique without making any technical modifications to its app. During its inception, the service promoted itself using fraternity parties (parties organised by an organisation of male studies at a college or university, particularly in the USA) at the University of Southern California, in which guests of said parties were required to download the Tinder mobile app as the price of admission. Relying on peer pressure, and regardless of whether guests at these parties were interested in the product or not, the tactic dramatically increased searches and downloads for the mobile app in a very short period of time. Search engine algorithms picked up on this spike in interest and in just 5 months Tinder’s mobile app was included in the iTunes top 100 apps list , and in 2 years had 4.7 billion ratings on user profiles – a rating meaning another profile submitting their interest in another profile (Peters, 2014). Tinder’s highly positive case study with growth hacking reinforces the point that growth hacking is completely detached from the product; its simple aim is to generate lots of web traffic very quickly. As a result of doing nothing more than forcing party guests to download their app, their search engine rankings increased dramatically with no technical or digital marketing involved. Regardless of how detailed their search engine optimisation efforts on their mobile app and marketing website were, Tinder proved in this success story that search engines value user attention above all else. If a particular website or app is achieving high volumes of searches, search engines will believe the product is of a high quality and allow more users to access it.
With such wildly different approaches to driving traffic to a website between common growth hacking techniques, it’s difficult to determine a solution which would measure the effectiveness of them all. In the media, growth hacking techniques are promoted with the use of positive case studies and statistics that may not accurately reflect how these techniques will perform on other websites, particularly as many articles regarding growth hacking may have a media bias.
2.4 Benefits and drawbacks to Growth Hacking
With such a wide range of techniques that utilise different platforms, it is difficult to discuss the benefits and drawbacks of growth hacking as a whole. The term describes a concept or area of digital marketing that is comprised of implementations which may benefit certain types of websites in different ways. While looking at the case study for Airbnb, in which Craigslist scraping is utilised, the benefits are clear; Airbnb can target an audience across more than one platform which increases the company’s chance of achieving a conversion (here meaning that a user has become a customer). However, it is unlikely that this technique will work when implemented on any website. For example, a journalism website may not find much use in scraping web pages for information, and may implement a technique similar to Groupon in which articles are locked until a number of social media shares have been made.
One major drawback to growth hacking can be the aftermath of receiving large quantities of web traffic. An adequate metaphor for growth hacking could be ‘throwing mud at the wall, hoping some of it will stick’ – here meaning that it does not matter how much traffic arrives at a particular website, it’s not guaranteed that these users will convert into customers.
2.5 Discussion of ethics in Growth Hacking
Ethics are widely considered to be relative to the person making the ethical decision (Mizzoni, 2017) and as such it can be unclear to determine what is ethically correct and what is not. Ethics closely links to an individual’s morals – here meaning what an individual considers to be ethically right and what is ethically wrong – therefore speaking about the ethics of growth hacking may sometimes appear to be subjective. To make the question of ethics when it comes to digital marketing and SEO slightly less ambiguous, websites such as social media platforms and search engines use guidelines, terms of service agreements and legal documents to specify how these websites should be used and interacted with. As stated previously, Airbnb, in implementing their growth hacking technique on Craigslist, violated a terms of service agreement by creating a web scraper or ‘bot’ that found listings on Craigslist for lodgings and contacted the users to advertise posting the listing on Airbnb for greater exposure. While this technique unquestionably assisted in Airbnb’s explosive growth – with little to no cost involved – it violated Craigslist’s terms of service and can be considered as spam (Brown, 2014), particularly as some users did not even expose their email address yet still received unwarranted soliciting from Airbnb.
In another case study of social news site Reddit, the technique used to growth hack was ‘self-population’ (Peters, 2014), a term which describes the act of creating fake user accounts in order to make a website seem more active and populated than it actually is. This technique reduces the intimidation factor for new users visiting the site; if a user tries to access a website with no active members, they might fear being the first to participate or fail to see the point in participating when there is no user interaction present. Both ideas can cause immediate failure for a website like Reddit, where a heavy focus is placed on social interaction. The technique of self-populating is arguably dishonest and raises an important issue as far as ethics are concerned. While this growth hacking technique was critical for Reddit to attract web traffic, their community was began with deception.
Ellis states himself in a blog post comment that, under his belief, the term growth hacker has been warped since its coining in 2010, claiming “external perceptions” of the term position it to be associated with ‘black hat marketers’ (Ellis, 2013). The appropriation of the term has somewhat changed its meaning to reflect bad ethical practice when implementing certain techniques, such as those by Airbnb which are classified as spam. Growth hacking’s original meaning, as discussed earlier in this paper, is to drive growth within a business, specifically – in the context of the web – traffic towards a particular website. There is no mention of techniques or methodologies, just a concept or a philosophy, therefore it could be suggested that the ethical ambiguity lies with the implementations of techniques devised using growth hacking as a concept, and not growth hacking itself.
3. Output design
3.1 Concept
As mentioned in the literature review, growth hacking techniques vary in their effectiveness and, as a result of a wide range of implementations, it can be difficult to measure this. For the practical implementation of the research put forward by this paper, an application to measure common growth hacking techniques’ effectiveness will be built. This application, accessed through a web browser, will provide solutions to enable users to drive traffic to their websites using growth hacking techniques. Through integrations with the website itself and external websites such as social media platforms, a certain degree of effectiveness would be measured, and a ‘score’ of how effective the solution was can be put forward to the user. This would be complete with a report detailing some useful metrics such as the origin of traffic (in terms of referrer such as Facebook or email link), the time taken from implementing techniques to users accessing the website, and how many users have been converted to a customer on the website.
3.2 Features
Techniques would be automatically and anonymously rated once results begin to come in, providing an easy way to see which techniques have been most effective for businesses using the application. As techniques promoted on some websites may only work for some businesses, such as those which post positive case studies, it would be useful for users to see exactly how effective these techniques are across all businesses from an objective standpoint – without media bias.
Additionally, tools could be provided with the application to create sharing and referral tools for a website. The application could generate some code for a user to include on their website which provides a link to share on social networks or send to their friends, which the application would be able to track through the use of social media bots (detecting posts made with specific information) and referral links (unique URL parameters that identify the origin of the link). A user could setup a ‘lockable’ feature, such as a webpage or purchase button, that the application could unlock after a specific amount of shares or referrals have been made.
3.3 Using Growth Hacking on a Growth Hacking Tool
Furthermore, growth hacking techniques could be included here to gain web traffic to this application, utilising smallprint (in the same way as email signatures, perhaps below the embedded code on a website) or creating backlinks to the application’s marketing website. This implementation would mean the growth hacking technique provided to its users would also be sourcing web traffic for the application at no cost to itself – the more it is used, the more exposure the application gets.
[i] Reading Google Trends charts: Numbers on the Y axis represent popularity in percentage; a value of 100 would denote the term's peak popularity in the given time period, whereas a value of 50 would denote the term’s popularity being half as what it was at 100. A value of 0 represents a lack of data during a specific time period.
[ii] Reading Google Trends charts: As above
References and further information
Original References
References
Ahmed, I., Shahzad, R. K., Rehman, K.-u. & Shabbir, J., 2013. Search Engine Optimisation: Evidence From Pakistan. Asian Academy of Management Journal, 18(2), pp. 1-16.
Arora, S., 2016. 5 Growth Hacking Case Studies and What You Can Learn From Them. [Online]
Available at: https://buildfire.com/growth-hacking-case-studies-learn/
[Accessed 05 11 2018].
Brown, M., 2014. Airbnb: The growth story you didn't know. [Online]
Available at: https://growthhackers.com/growth-studies/airbnb
[Accessed 22 10 2018].
Chen, A., 2014. Growth Hacker is the new VP Marketing. [Online]
Available at: https://andrewchen.co/how-to-be-a-growth-hacker-an-airbnbcraigslist-case-study/
[Accessed 17 10 2018].
Ellis, S., 2010. Find a Growth Hacker for Your Startup. [Online]
Available at: http://www.startup-marketing.com/where-are-all-the-growth-hackers/
[Accessed 18 10 2018].
Ellis, S., 2013. Growth Hacking is Bullshit. [Online]
Available at: https://growthhackers.com/articles/growth-hacking-is-bullshit#comment-3861
[Accessed 30 10 2018].
Ellis, S., 2014. Ask GH: Was there something unethical about Airbnb's Craigslist growth hack?. [Online]
Available at: https://growthhackers.com/questions/ask-gh-was-there-something-unethical-about-airbnbs-craigslist-growth-hack/
[Accessed 21 10 2018].
Ellis, S., 2014. Via Twitter, @DHH wrote: "Growth hacking: A cool-sounding euphemism for making the doer feel good about using the same old sleazy marketing tricks". [Online]
Available at: https://growthhackers.com/articles/dhh-growth-hacking-a-cool-sounding-euphemism-for-making-the-doer-feel-good-about-using-the-same-old-sleazy-marketing-tricks#comment-3803
[Accessed 10 October 2018].
Fishkin, R., 2018. Lost and Founder: a Painfully Honest Field Guide to the Startup World. 1st ed. New York: Portfolio/Penguin.
Geru, M., Rusu, E. & Capatina, A., 2014. Growth Hacking Practices in a Start-up: A Case Study on thecon.ro. Risk in Contemporary Economy, p. 212.
Goldhaber, M. H., 1997. The Attention Economy and the Net. First Monday, 2(4).
Google, 2018. Google Trends. [Online]
Available at: https://trends.google.com/trends/explore?date=all&q=growth%20hacker
[Accessed 13 11 2018].
Google, 2018. How Google Search Works. [Online]
Available at: https://support.google.com/webmasters/answer/70897?hl=en&ref_topic=3309469
[Accessed 27 10 2018].
Google, 2018. Link schemes. [Online]
Available at: https://support.google.com/webmasters/answer/66356?hl=en
[Accessed 04 11 2018].
Halavais, A. M. C., 2018. Search engine society. 2nd ed. Cambridge: Polity Press.
Holiday, R., 2013. Growth Hacker Marketing: a Primer on the Future of PR, Marketing and Advertising. London: Profile Books.
Hoque, F., 2012. Why Most Venture-Backed Companies Fail. [Online]
Available at: https://www.fastcompany.com/3003827/why-most-venture-backed-companies-fail
[Accessed 27 10 2018].
Lee, S., Jang, W., Lee, E. & Oh, S. G., 2016. Search engine optimization. Library Hi Tech, 34(2), pp. 197-206.
Lehr, A., 2017. What Is the Difference Between White Hat and Black Hat SEO?. [Online]
Available at: https://www.searchenginejournal.com/white-vs-black-hat-seo-what-is-the-difference/183088/
[Accessed 10 October 2018].
Lella, A., 2016. Comscore Releases February 2016 U.S. Desktop Search Engine Rankings. [Online]
Available at: https://www.comscore.com/Insights/Rankings/comScore-Releases-February-2016-US-Desktop-Search-Engine-Rankings
[Accessed 21 10 2018].
Lerner, C., 2017. Explosive Growth: A Few Things I Learned While Growing To 100 Million Users - And Losing $78 Million. 1st ed. Place of publication not identified: Clifford Ventures Corporation.
Malkin, E. G., 1996. Internet Users' Glossary. [Online]
Available at: https://www.rfc-editor.org/rfc/rfc1983.txt
[Accessed 3 11 2018].
McRedmond, B., 2014. Growth Hacking is Bullshit. [Online]
Available at: https://www.intercom.com/blog/growth-hacking-is-bullshit/
[Accessed 10 October 2018].
Mizzoni, J., 2017. Ethics.. 2nd ed. Somerset: John Wiley & Sons, Incorporated.
Moz, 2018. Backlinks. [Online]
Available at: https://moz.com/learn/seo/backlinks
[Accessed 22 10 2018].
Penenberg, A., 2010. Viral loop: the power of pass-it-on. London: Sceptre.
Peters, R., 2014. Growth hacking techniques, disruptive technology: how 40 companies made it big - online growth hacker marketing strategy. s.l.:World Ideas Incorporated.
Statista, 2018. Number of monthly active Facebook users worldwide as of 2nd quarter 2018 (in millions). [Online]
Available at: https://www.statista.com/statistics/264810/number-of-monthly-active-facebook-users-worldwide/
[Accessed 30 10 2018].
Tillison, M., 2017. Why Link Farming Is Not Effective SEO Link Building. [Online]
Available at: https://tillison.co.uk/blog/link-farming-not-effective-seo-link-building/
[Accessed 04 11 2018].
Wilson, R. F. & Pettijohn, J. B., 2006. Search engine optimisation: A primer on keyword strategies. Journal of Direct, Data and Digital Marketing Practice, 8(2), pp. 121-133.
